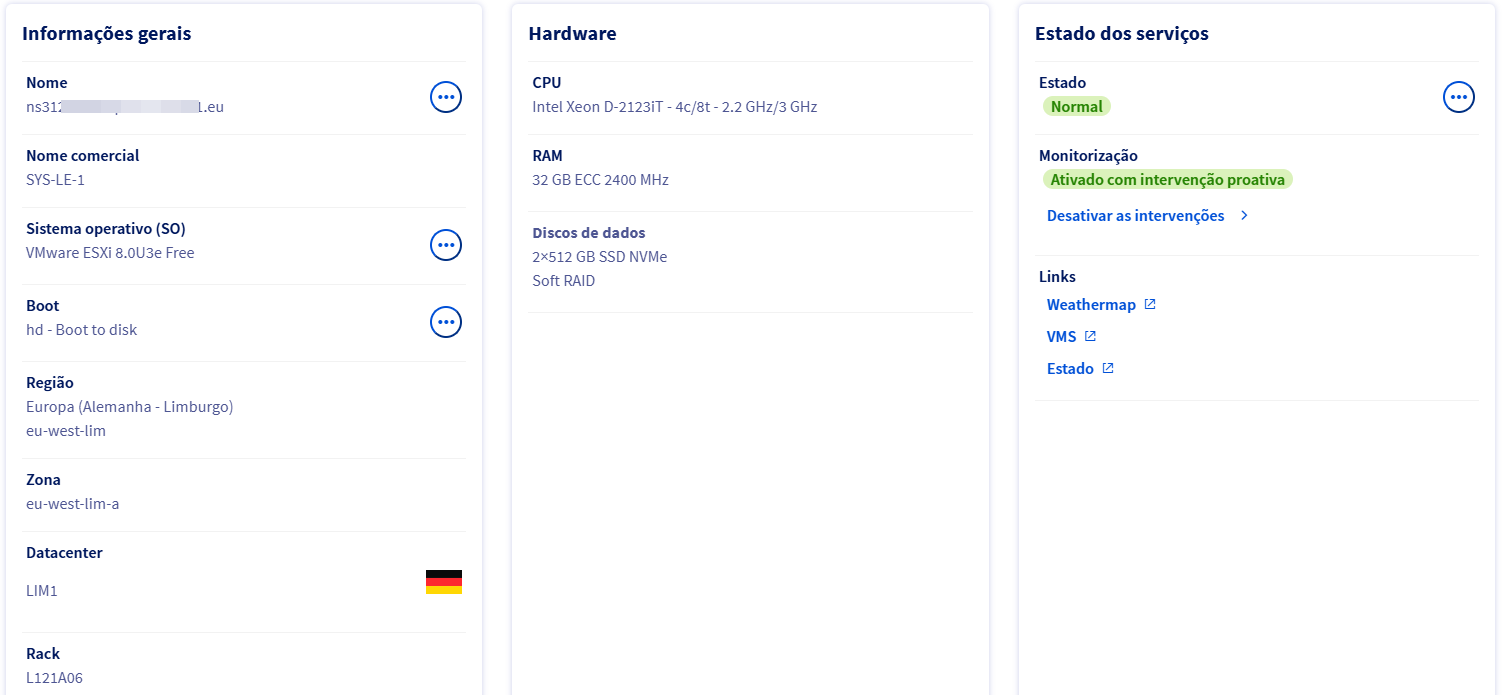
Objective evidence of a real, active and segmented infrastructure
This page gathers verifiable technical evidence demonstrating that the infrastructure presented in this portfolio has been operated in a real environment.
The evidence below can be externally validated or inferred from technical behaviors that cannot be realistically simulated without an actual infrastructure.
Access to the site occurs through the Cloudflare network, responsible for TLS termination and edge protection.
$ curl -I https://alexandraidc.com
HTTP/1.1 200 OK
Server: cloudflare
CF-RAY: 9b7bc4cfba26d382-FRA
cf-cache-status: DYNAMIC
alt-svc: h3=":443"; ma=86400
The headers Server: cloudflare and CF-RAY
confirm that the request was processed at Cloudflare’s edge.
The suffix -FRA indicates the point of presence (Frankfurt).
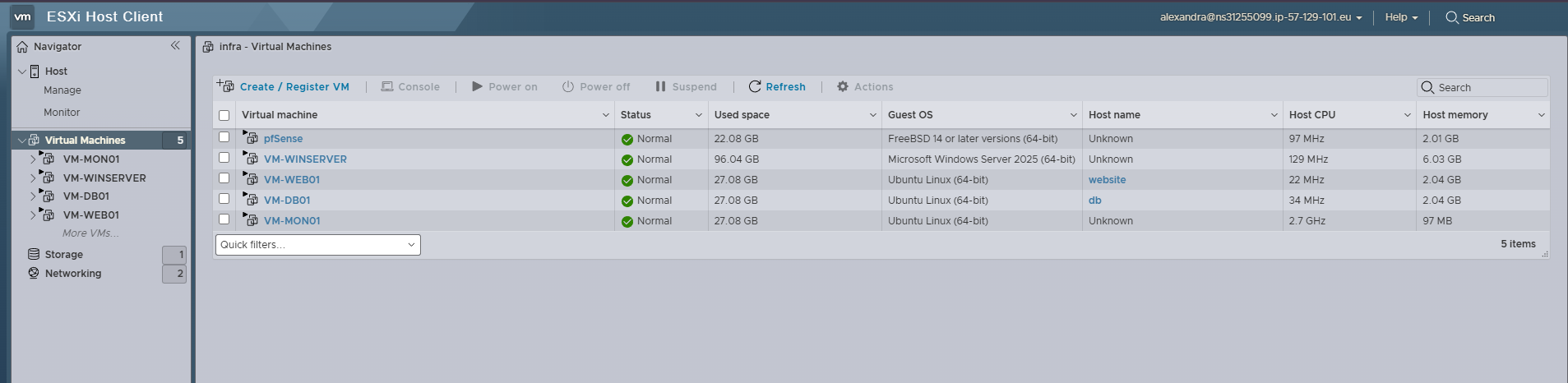
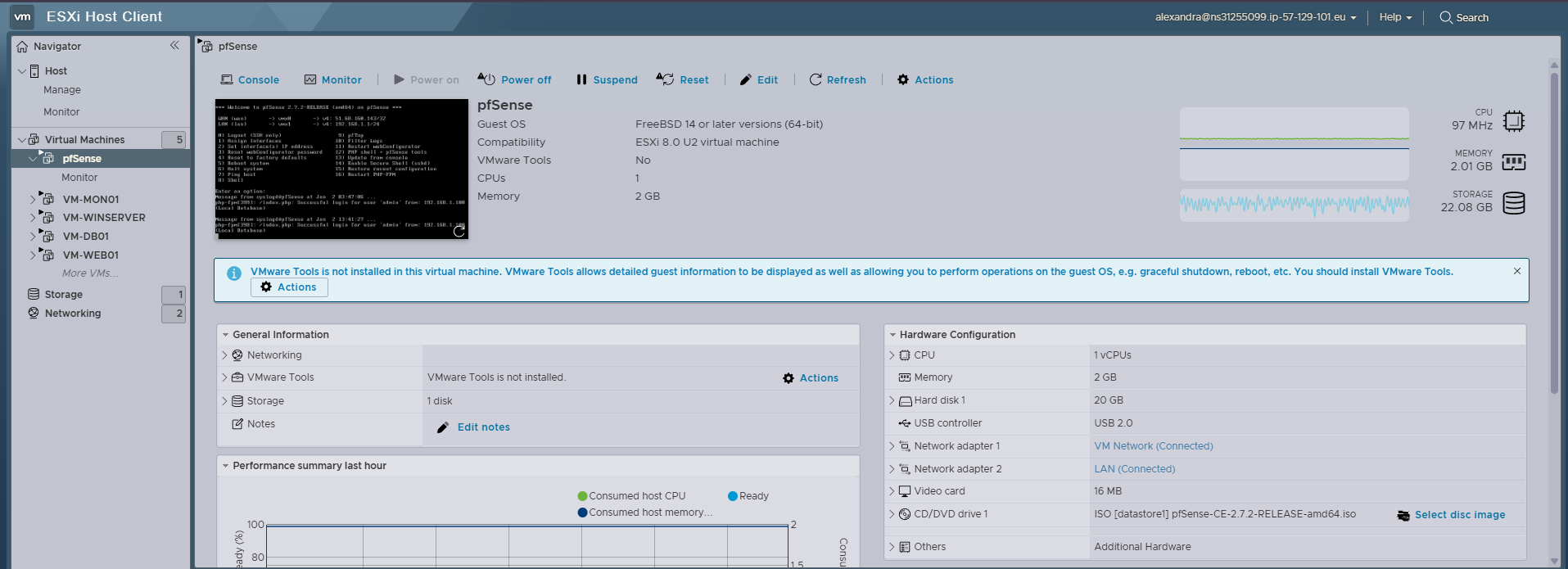
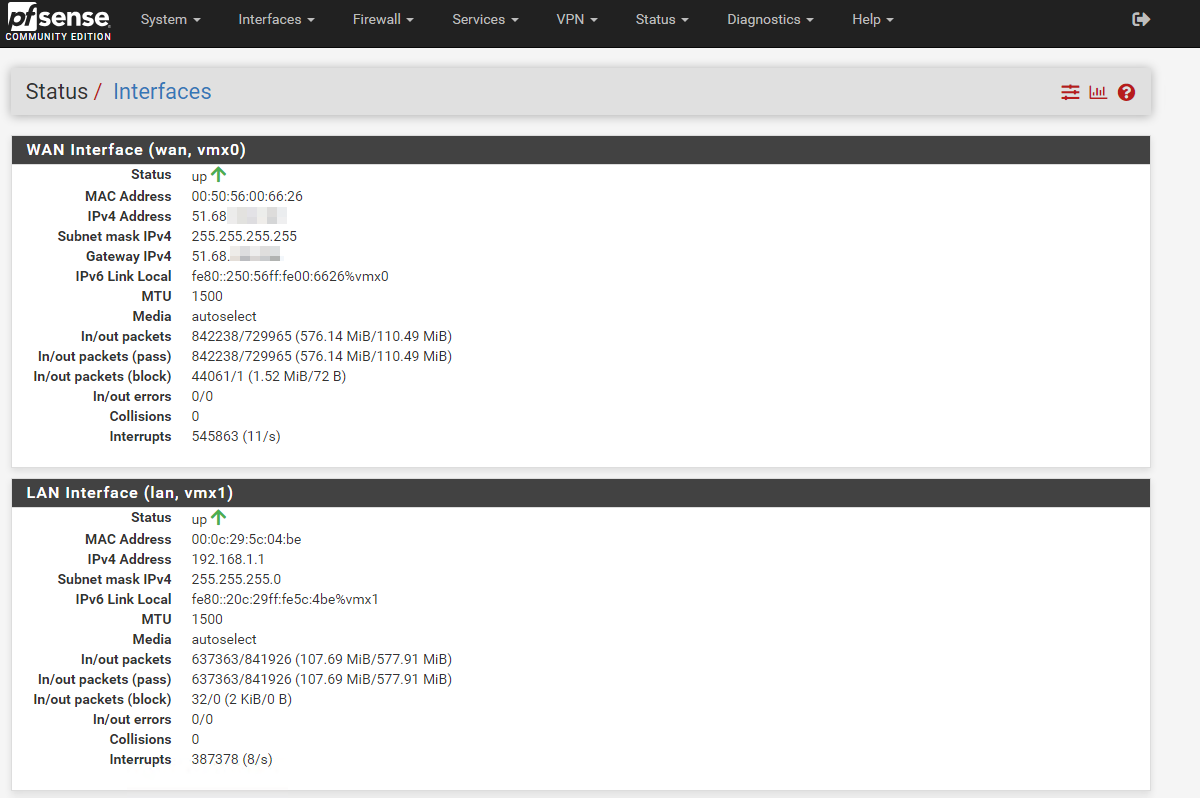
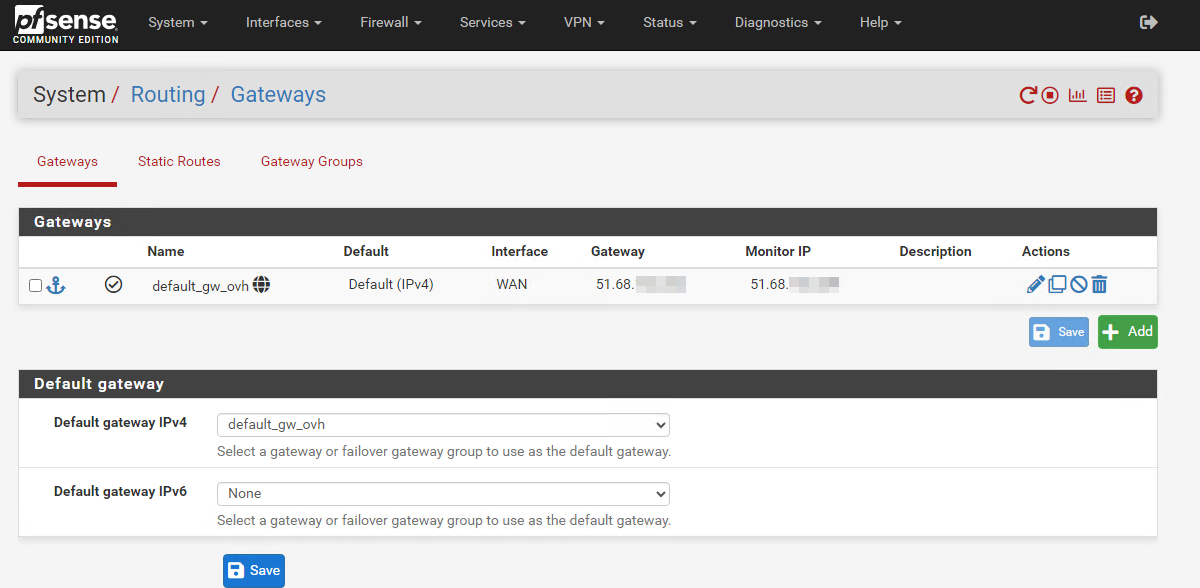
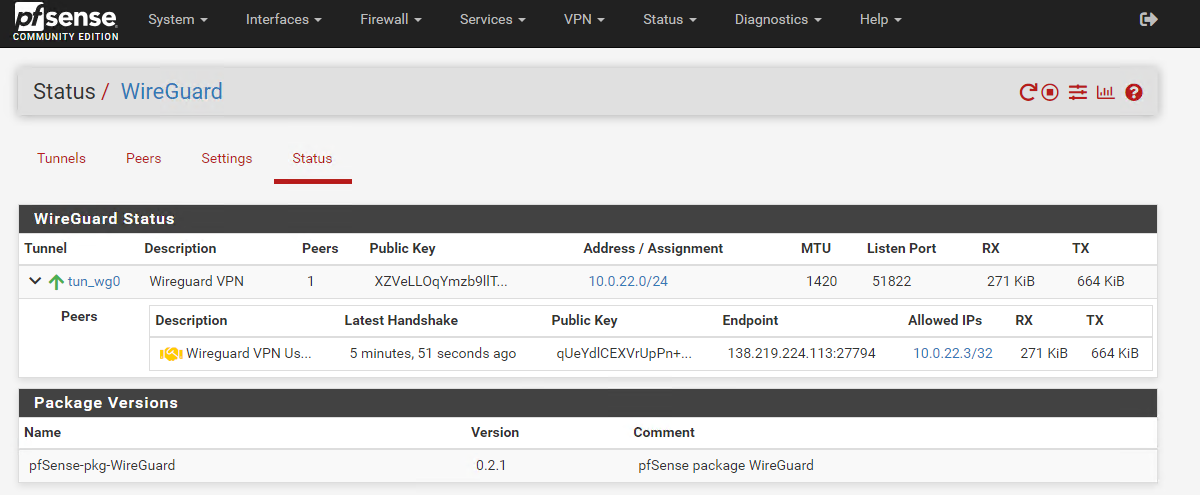
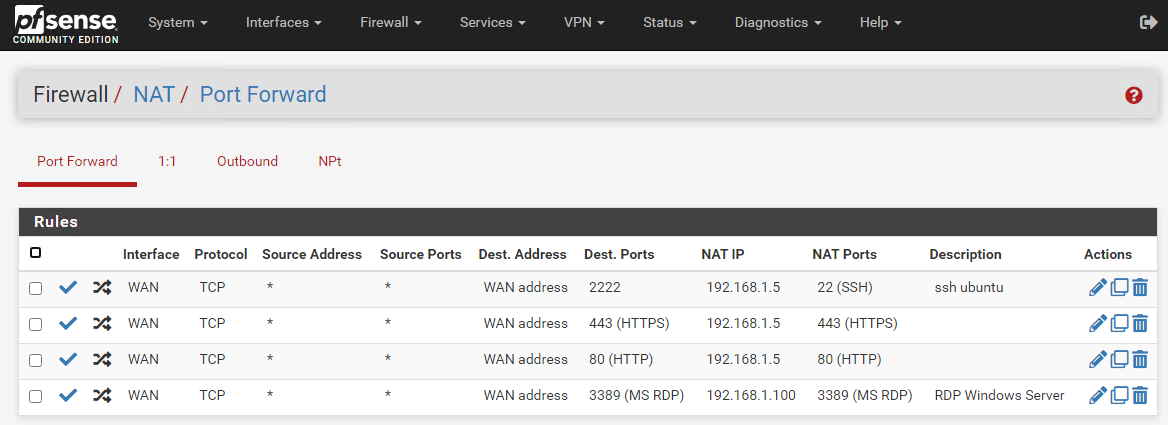
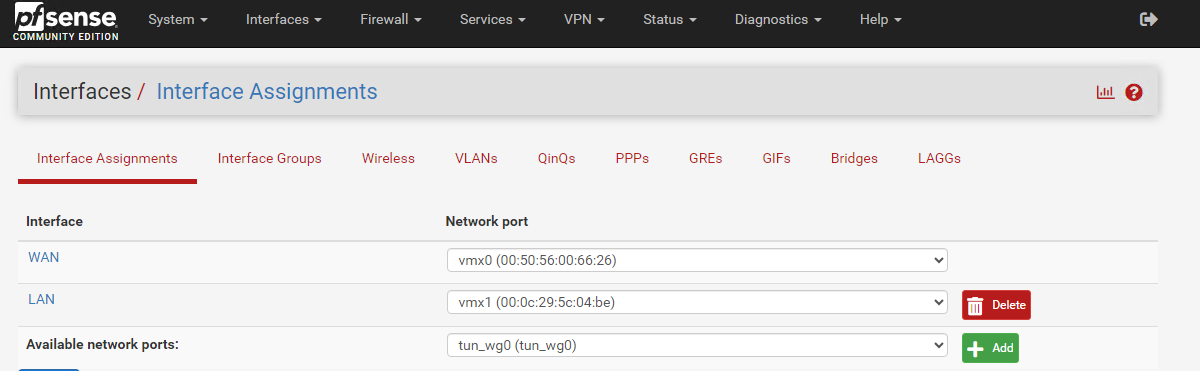
The application does not have a direct public IP. Service exposure occurs exclusively through a perimeter firewall, responsible for performing NAT / Port Forward to a VM within a private network.
This model centralizes access control, eliminates direct VM exposure, and is characteristic of dedicated firewalls such as pfSense.
Cloudflare does not perform NAT and the web server does not have a public IP, which implies the presence of an intermediate firewall.
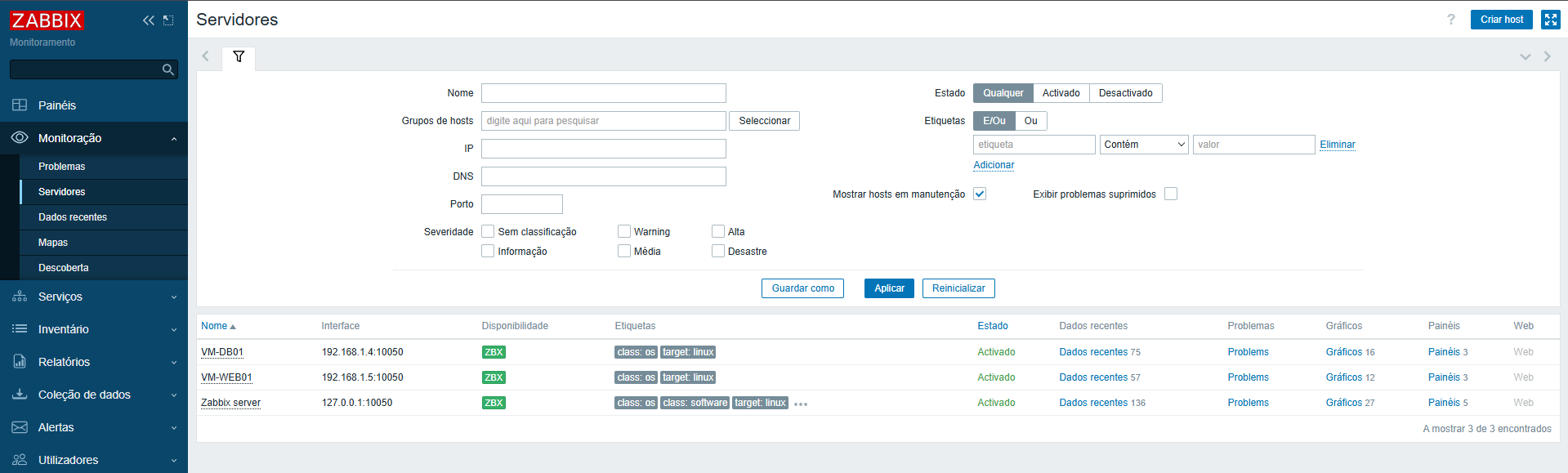
The application, database, and monitoring VMs operate exclusively within a private network, with no direct external access.
This level of isolation cannot be achieved through application configuration alone, requiring network-layer control.
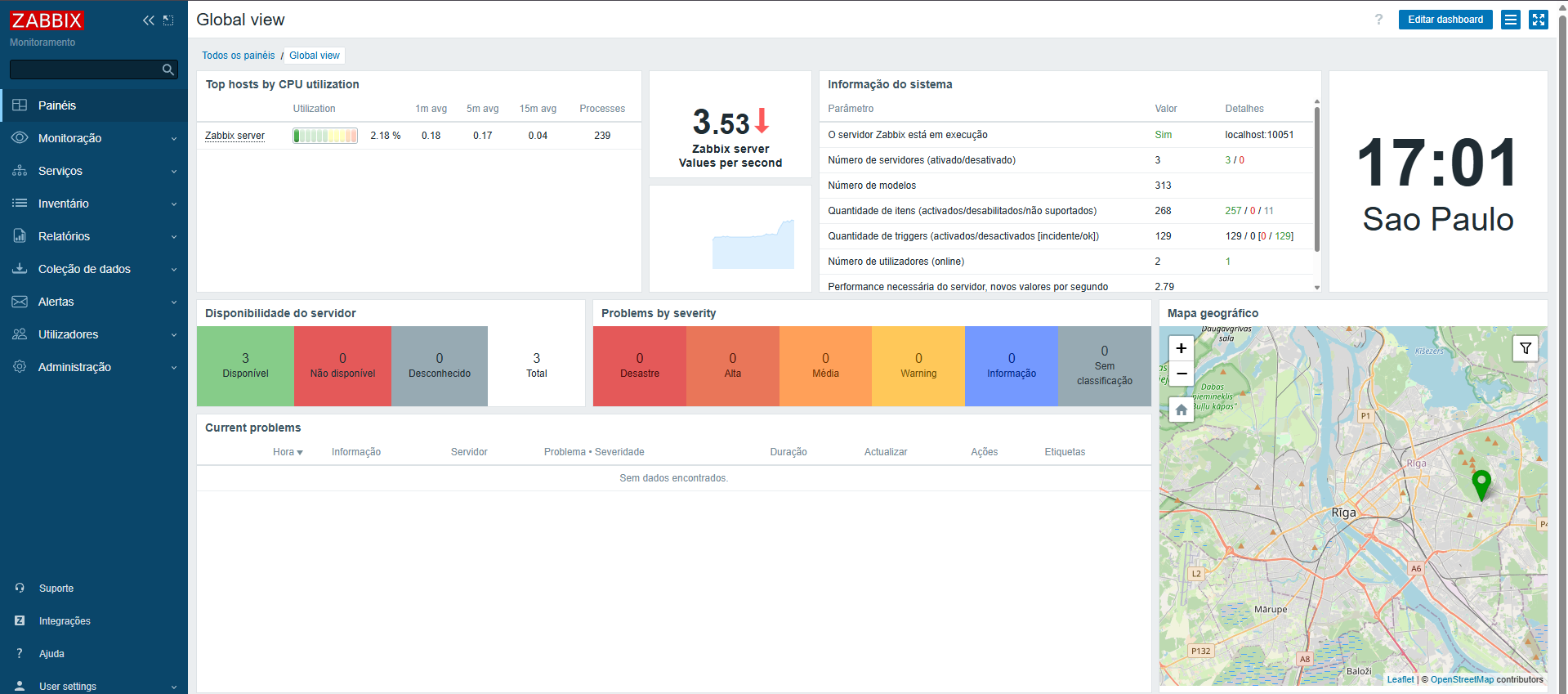
The environment is continuously monitored by internal systems, tracking availability, service status, and operational metrics.
The monitoring system operates within the internal network with no public exposure.
Below are real visual records of the environment. The images use standardized size and proportions to preserve visual consistency and avoid distortion.